Postfix
Postfix is a free and open source mail transfer agent (MTA). Postfix is secure, performs well and has good spam filtering options.
We also recommend you to use Spamassassin and Amavis to protect mail servers from spammers.
Sisällysluettelo
- 1 Installation
- 2 Configuration
- 3 Additional settings
- 4 Test Postfix functionality
- 5 Protecting your mail server
- 6 Postfix toiminta PHP5 kanssa
- 7 Virheilmoituksia
- 7.1 Sender address rejected: Domain not found (in reply to RCPT TO command
- 7.2 Client host rejected: Access denied
- 7.3 connect to mx3.hotmail.com[65.55.37.104]:25: No route to host
- 7.4 Host or domain name not found. Name service error for name=gmail.con type=A: Host not found
- 7.5 Invalid mail address, must be fully qualified domain (in reply to RCPT TO command))
- 7.6 unable to verify address (in reply to MAIL FROM command))
- 8 Lähteet
Installation
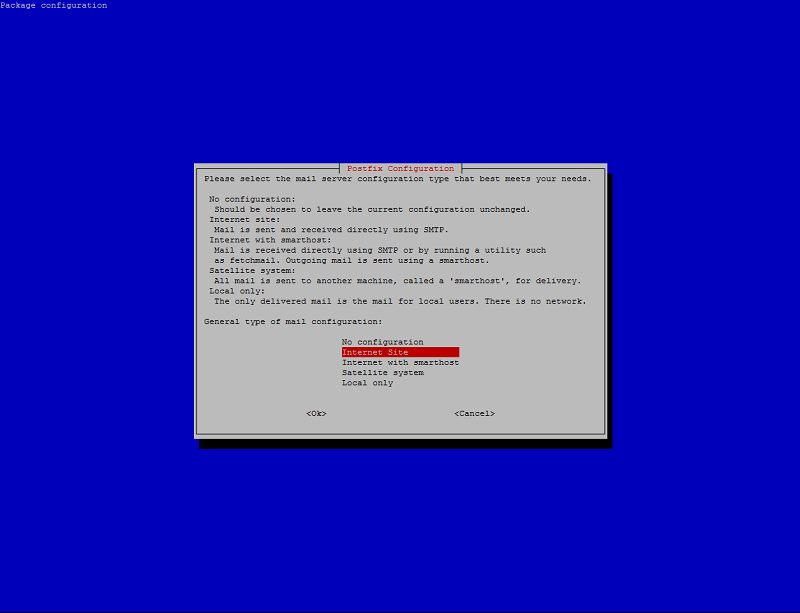
aptitude install postfix
Follow the installation programs instructions.
After this you need to give the servers host name.
For example:
mail.example.com
Configuration
Open the configuration file:
nano /etc/postfix/main.cf
Check that the postfix configuration file has defined the computers' host name and server address.
myhostname = server.example.com alias_maps = hash:/etc/aliases alias_database = hash:/etc/aliases myorigin = example.com mydestination = example.com, server.example.com, localhost, localhost.example.com$ #relayhost = mynetworks = 127.0.0.0/8 [::ffff:127.0.0.0]/104 [::1]/128 mailbox_command = procmail -a "$EXTENSION" mailbox_size_limit = 0 recipient_delimiter = + inet_interfaces = all
Save the file and then open the next file
nano /etc/postfix/master.cf
By default, normal SMTP connections are allowed in port 25 by the master.cf file.
smtp inet n - - - - smtpd
By default the next lines will be marked by a number sign (#).
Enable SMTP transfer in port 587 by erasing the number sign. It can also transfer encrypted traffic with the STARTTLS command.
submission inet n - - - - smtpd -o syslog_name=postfix/submission -o smtpd_tls_security_level=encrypt -o smtpd_sasl_auth_enable=yes -o smtpd_client_restrictions=permit_sasl_authenticated,reject -o milter_macro_daemon_name=ORIGINATING
Enable SMTPS traffic in port 465 by removing the number sign. SSL encryption is enabled by default in this connection. SASL certification is recommended to be used.
smtps inet n - - - - smtpd -o syslog_name=postfix/smtps -o smtpd_tls_wrappermode=yes -o smtpd_sasl_auth_enable=yes -o smtpd_client_restrictions=permit_sasl_authenticated,reject -o milter_macro_daemon_name=ORIGINATING
Explanations:
Your servers' name (make sure it is the same as hostname (command: hostname)):
myhostname = server.example.com
Log in credentials = Same as Debian. Let's not change.
alias_maps = hash:/etc/aliases alias_database = hash:/etc/aliases
Domain (define your server into a mail address [email protected]). By default there is defined /etc/mailname:
myorigin = example.com
Computer host names:
mydestination = example.com, server.example.com, localhost, localhost.example.com$ #relayhost = 127.0.0.1:10111
This is required if you don't have direct connection to the network.
As example, a mail server from Sonera:
relayhost = [mail.inet.fi]:25
DNA post server:
relayhost = [smtp.dnainternet.net]:25
Your local network:
mynetworks = 127.0.0.0/8 [::ffff:127.0.0.0]/104 [::1]/128 mailbox_command = procmail -a "$EXTENSION" mailbox_size_limit = 0 recipient_delimiter = +
Network connections:
inet_interfaces = all
Close the file and restart postfix.
service postfix restart
Additional settings
Virtual e-mail addresses
You can direct your virtual mail addresses e.g. [email protected] and [email protected] to your own user.
Open the file:
/etc/aliases
# /etc/aliases mailer-daemon: postmaster postmaster: root nobody: root hostmaster: root usenet: root news: root webmaster: root www: root ftp: root abuse: root noc: root security: root root = [username]
By changing [username] into your own account, you can get all the mail from these user accounts in the same inbox. You can add other addresses to the end of the file:
[alias_postname] = [touser]
Confirm changes
newaliases
Virtual domains
Virtualdomains are meant for mail servers that send and receive for multiple different domains.
Open the postfix configuration file main.cf
/etc/postfix/main.cf
Add the following lines:
virtual_alias_domains = example.com virtual_alias_maps = hash:/etc/postfix/virtual
Create a new file
[email protected] postmaster [email protected] matti [email protected] kalle # Uncomment entry below to implement a catch-all address # @example.com aleksi
Don't add virtual_alias_domain as a mydestination domain!
Mail redirection
For example, how to redirect mail from [email protected] to matti.example2.com
Open the postfix configuration file main.cf
/etc/postfix/main.cf:
Add the following lines into the file:
virtual_alias_domains = example.com virtual_alias_maps = hash:/etc/postfix/virtual
Create a new file
/etc/postfix/virtual:
Add the following lines into the file
[email protected] postmaster [email protected] [email protected] [email protected] [email protected] # Uncomment entry below to implement a catch-all address # @example.com jim@yet-another-site
The domain of mail to be redirected must also be mydestination marked. You can't, for instance, redirect aliases /etc/alias
Check configuration
postmap /etc/postfix/virtual
Test Postfix functionality
We send a test mail:
Install this e-mail tool if you haven't done so yet:
apt-get install mailutils
and after that we send some mail:
mail [email protected]
The command will print:
Subject: your mail's topic or headline
After this write your message and hit enter, and it will print:
CC:
Which you can leave blank. Send the mail by the keyboard combination CTRL+D.
Protecting your mail server
When you create your own mail server, you must immediately set up basic protection to cover yourself from spammers. We also recommend that you enable SASL proofing.
Filtering spam
By adding a few lines to the configuration we can verify if the sender's host name / domain actually exists, and block it if it doesn't.
nano /etc/postfix/main.cf
smtpd_recipient_restrictions = reject_invalid_hostname,
reject_unknown_recipient_domain,
reject_unauth_destination,
reject_rbl_client sbl.spamhaus.org, # If your provider is Sonera, do not add this line
permit
smtpd_helo_restrictions = reject_invalid_helo_hostname,
reject_non_fqdn_helo_hostname,
reject_unknown_helo_hostname
And this checks the list of known spam senders for cross-reference:
nano /etc/postfix/main.cf
smtpd_client_restrictions = reject_rbl_client dnsbl.sorbs.net
SMTPS SASL proofing
By adding the following line you prevent e-mail transfer from other networks than your own. Using SASL proofing you can also send from other networks.
nano /etc/postfix/main.cf
smtpd_recipient_restrictions = permit_mynetworks, permit_sasl_authenticated, reject
nano /etc/postfix/master.cf
Remove the number sign (#) from the lines with submission and smtps. If you also want authentication, add the following line below those.
-o smtpd_sasl_auth_enable=yes -o smtpd_client_restrictions=permit_sasl_authenticated,reject
TLS (STARTSSL)
Example of the configuration file /etc/postfix/main.cf
smtpd_tls_cert_file = /etc/postfix/cert.pem smtpd_tls_key_file = /etc/postfix/key.pem smtpd_tls_mandatory_ciphers = high smtpd_tls_mandatory_exclude_ciphers = aNULL, MD5 smtpd_tls_security_level = encrypt smtpd_tls_mandatory_protocols = !SSLv2, !SSLv3 smtpd_tls_mandatory_protocols = TLSv1 TLSv1.1 TLSv1.2 smtpd_tls_ask_ccert = yes smtp_tls_fingerprint_digest = sha1 smtpd_use_tls=yes
Enable Submission by removing the number signs (#).
Test STARTSSL: https://starttls.info/
and
SMTPS
Postfix has support for SSL connections with TLS but not with only SSL. Thus, the following instruction is only for SSL, but if you have support for TLS encryption, it is recommended to use it.
Instruction source: http://www5.sonera.fi/keskustele/viewtopic.php?f=59&t=9210 (Finnish)
SMPTS is a secure SMTP connection and the current standard recommendation is to use it.
In this example we are on the Sonera (ISP) network:
Olet siis konfiguroinnut /etc/postfix/main.cf tiedostoon. Tämä siis toimii salaamattassa portissa 25.
relayhost = [mail.inet.fi]
It is now time to move to secure e-mail, which is a bit more difficult as Sonera's own post servers do not support TLS encryption. Postfix does not support SSL encryption, but we install a tiny workaround and it will work.
First we install Stunnel
aptitude install stunnel
We create the file /etc/stunnel/postfix.conf and copy the lines below into it:
[ssmtp_c2s] accept = 127.0.0.1:10111 client = yes connect = mail.inet.fi:465 delay = yes
and after this you open the file /etc/default/stunnel and switch it to the following:
# Change to one to enable stunnel automatic startup # CHANGE #ENABLED=0 ENABLED=1 FILES="/etc/stunnel/*.conf" OPTIONS="" # Change to one to enable ppp restart scripts PPP_RESTART=0
After this, modify /etc/postfix/main.cf to the following:
relayhost = 127.0.0.1:10111
# SASL authentication
smtp_sasl_auth_enable=yes
smtp_sasl_password_maps = hash:/etc/postfix/passwd
smtp_sasl_security_options = noanonymous
smtp_sasl_tls_security_options = noanonymous
# TLS
smtp_tls_eccert_file =
smtp_tls_eckey_file =
# http://www.postfix.org/TLS_README.html#client_tls_may
smtp_tls_security_level = may
smtpd_tls_received_header = yes
tls_random_source = dev:/dev/urandom
# http://www.postfix.org/TLS_README.html#client_tls_may
smtpd_tls_security_level = may
Create file /etc/postfix/passwd and type your Sonera e-mail's username and password into it.
mail.inet.fi:465 USERNAME:PASSWORD
Esimerkiksi:
mail.inet.fi:465 [email protected]:taisto
Tämän jälkeen anna tämä komento:
postmap hash:/etc/postfix/passwd
Kokeile toimiiko antamalla seuraava komento:
postmap -q mail.inet.fi:465 /etc/postfix/passwd
Jos komento tulostaa käyttäjätunnuksesi ja salasanasi, kaikki toimii tähän asti
Estä muiden käyttäjien näkemästä salasanaasi:
chmod go-rwx /etc/postfix/passwd*
Käynnistä lopuksi palvelut uudelleen
service stunnel4 restart
service postfix restart
Postfix toiminta PHP5 kanssa
PHP5 sisältää mail funktion. Sinun tulee konfiguroida php.ini tiedostoa
nano /etc/php5/apache2/php.ini
ja muuttaa se tälläiseksi:
; For Unix only. You may supply arguments as well (default: "sendmail -t -i"). ; http://php.net/sendmail-path sendmail_path = "/usr/sbin/sendmail -t -i"
ja käynnistä apache uudelleen
service apache2 restart
Virheilmoituksia
Tässä lista yleisistä virheilmoituksista mitä ilmenee usein postfixin konfiguroinnista:
Sender address rejected: Domain not found (in reply to RCPT TO command
myorigin on määritetty väärin /etc/mailname tiedostosta. Tämän tulee olemaan domainin nimi.
myorigin /etc/mailname
example.com
Client host rejected: Access denied
Relayhost on estänyt sinut, ehkä roskapostien takia.
connect to mx3.hotmail.com[65.55.37.104]:25: No route to host
Tarkista Relayhost main.cf tiedostossa. Mahdollisesti sinulla on suljettu suoraan portti 25.
Host or domain name not found. Name service error for name=gmail.con type=A: Host not found
DNS Virhe. Tarkista resolv.conf tiedostossa määriteytyt DNS asetukset. Kokeile nslookup komentoa.
Invalid mail address, must be fully qualified domain (in reply to RCPT TO command))
Isäntänimessä ongelma. Varmista että DNS on oikein määritetty ja isäntänimi main.cf tiedostossa.
unable to verify address (in reply to MAIL FROM command))
DNS ongelma. Varmista että sinulla on määritetty oikein A-records DNS palvelimelle ja MX-records. Tarkista /etc/hosts tiedosto. Korjaus:
nano /etc/hosts
127.0.0.1 localhost mail.example.com server 127.0.1.1 example.com mail.example.com server